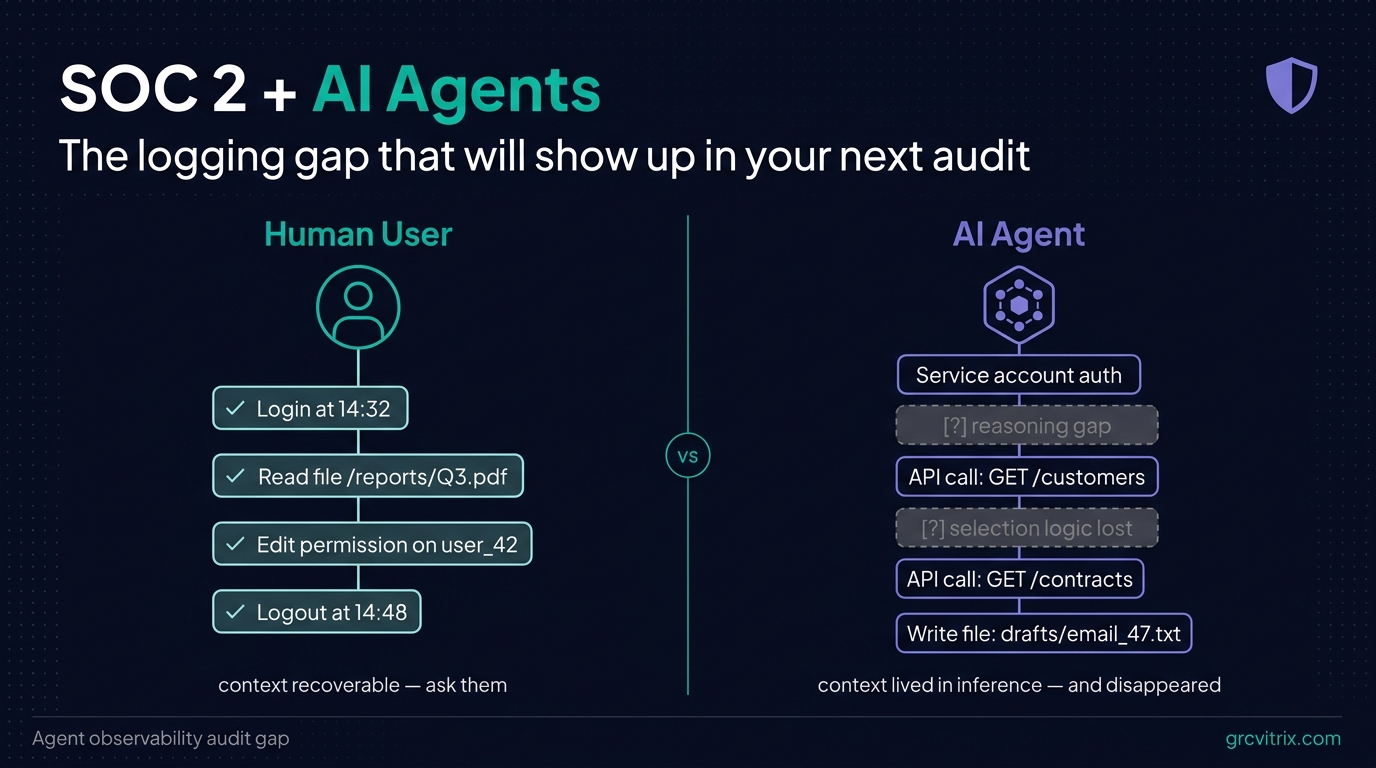
SOC 2 and AI Agents: The Logging Gap That Will Show Up in Your Next Audit
For about 20 years, SOC 2 logging worked because it answered one question: who did what, when? User logs in. Developer pushes code. Admin changes a permission. Every meaningful action traced back to a human identity. Every framework — SOC 2, ISO 27001, NIST 800-53 — assumed this. Logging infrastructure was built around it. AI agents are quietly breaking that assumption. If you’re shipping AI features on top of customer data — even just an internal automation that summarizes vendor contracts or routes support tickets — you’re running a system that takes actions, accesses data, and makes decisions. Your SIEM sees the API calls. It does not see what the agent was trying to do, why it picked one file over another, or what it produced as a result. ...